Symantec shares 2017’s Internet Security Threat Profile — Cryptojacking attacks has jumped 8500% in 2017!
Security is an increasing concern for everyone as we start using more and more connected devices and applications. We are entrusting more information to the cloud, in addition to relying to our connected devices to do everything from watching funny cat videos to handling online banking transactions. However it seems that cybercriminals aren’t targeting our personal data and bank information now. They have a much more lucrative way — cryptojacking.
Cryptojacking attacks shoot up inline with cryptocurrency value spike
The increase in cryptocurrency value has triggered a cryptojacking gold rush, as cybercriminals rush to use your hardware to mine the valuable coins. The detection of coinminers has increased by 8500% in 2017, and Symantec recorded a total of 1.7 million miners in December 2017. This number is inclusive of legit and malware miners, so it isn’t as bad as it sounds. Malaysia ranks seventh in the Asia-Pacific Japan region, and 26th globally in terms of crypto-mining activity. While legitimate miners are fine, miners which are injected can slow devices, increase power consumption and heat output, otherwise rendering devices unusable.
Aside from miners that run on your system natively, in-browser mining is also gaining popularity. It is as easy as installing a single line of code into the site’s script to get your system to mine for these cyber criminals. In-browser miners has shot up by 34000%. PCs aren’t the only targeted systems, with Macs also falling victim to browser-based miners. The increasing popularity of IoT devices are ripe targets for exploitation, with Symantec finding a 600% increase in IoT attacks in 2017.
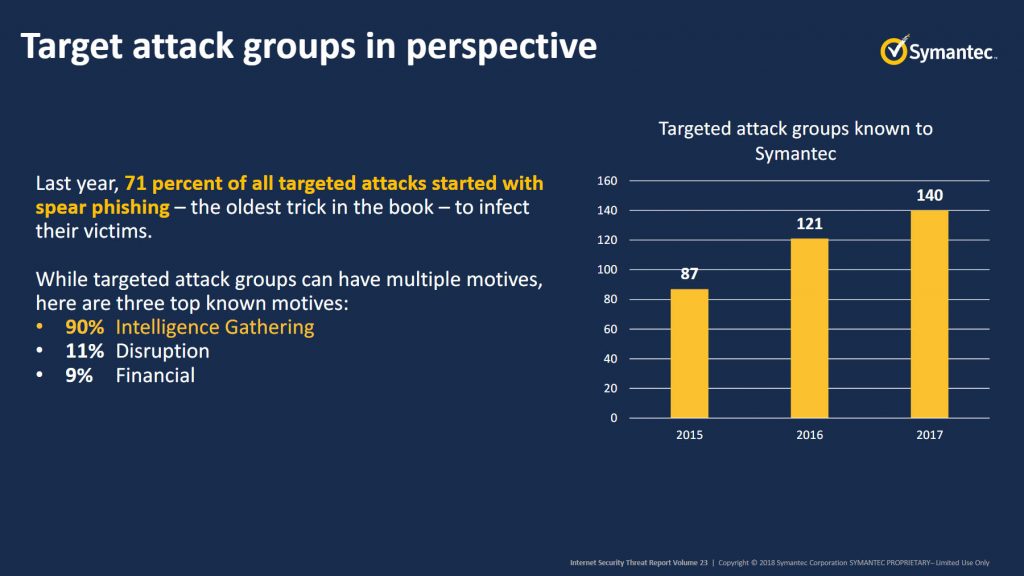
Targeted attackers are falling back to old tricks
Symantec is tracking 140 organized groups involved in targeted attacks. In 2017, 71% of all targeted attacks start with spear phishing. This is the oldest trick known, involving the victim unknowingly opening themselves up to attacks. Zero-day vulnerabilities are falling out of favor, as they are difficult to find as well as quickly patched. 90% of these attacks are used to gather more information about their victims, 11% are intended to disrupt, while 9% are financially motivated.
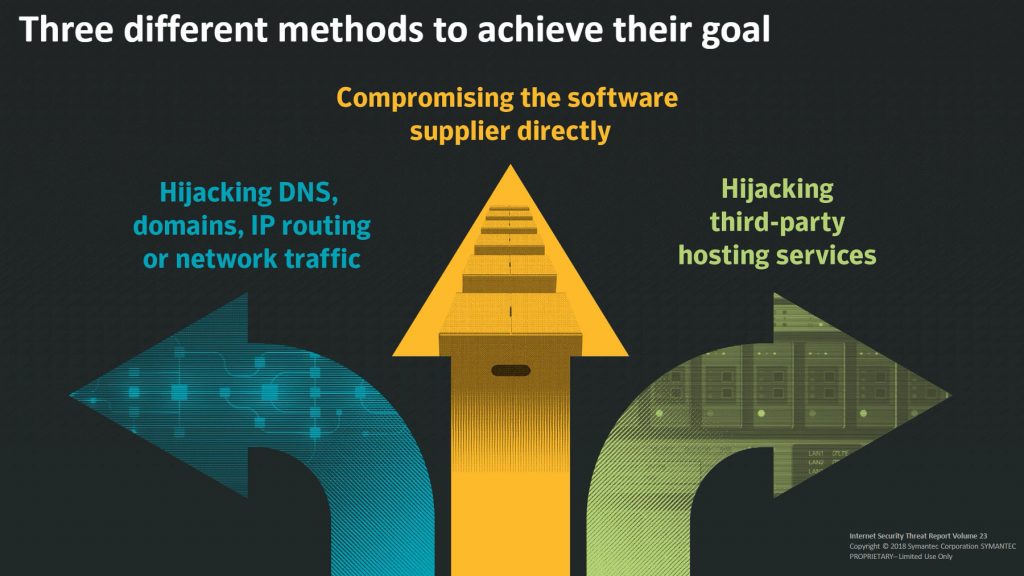
Your “safe” download source may not be as safe as you think
Attackers prefer attacking the software supply chain, implanting malware and injecting it into your system without you even knowing it. By implanting a piece of malware into an otherwise legitimate software package, even the savvier among us will be unable to catch the malware. The trojanized software is delivered from a trusted domain, digitally signed and via a trusted update process. But yet it delivers malware to your system. Hijacking the software supply chain also allows attackers to target certain industries that use specific software, which will be injected with malware.
Your smartphone may be an easy target
Mobile malware variants increased by 54% year-over-year. As everyone now carries a smartphone, mobile malware is an increasingly popular target. Older operating systems are also easier targets, and according to Symantec’s data, only 20% of Android devices are running the latest major version. This means 80% of all Android devices may be vulnerable to attacks, and that’s a lot of devices. Privacy is also a major issue, as older Android versions do not have the granular permission controls like the latest versions do. Users may be inadvertently allowing apps to take their information simply by installing the apps.
Ransomware underwent price adjustments in 2017
As ridiculous as that sounds, ransomware actually underwent a market correction. The average ransom cost has dropped to $522. The increase in competition among ransomware and also the shift to cryptojacking as a quick means to making a buck has reduced the ransom cost. Still, ransomware remains a real threat as the number of ransomware detected has not decreased significantly, and the number of ransomware variants has actually increased by 46% despite the reduced profitability.
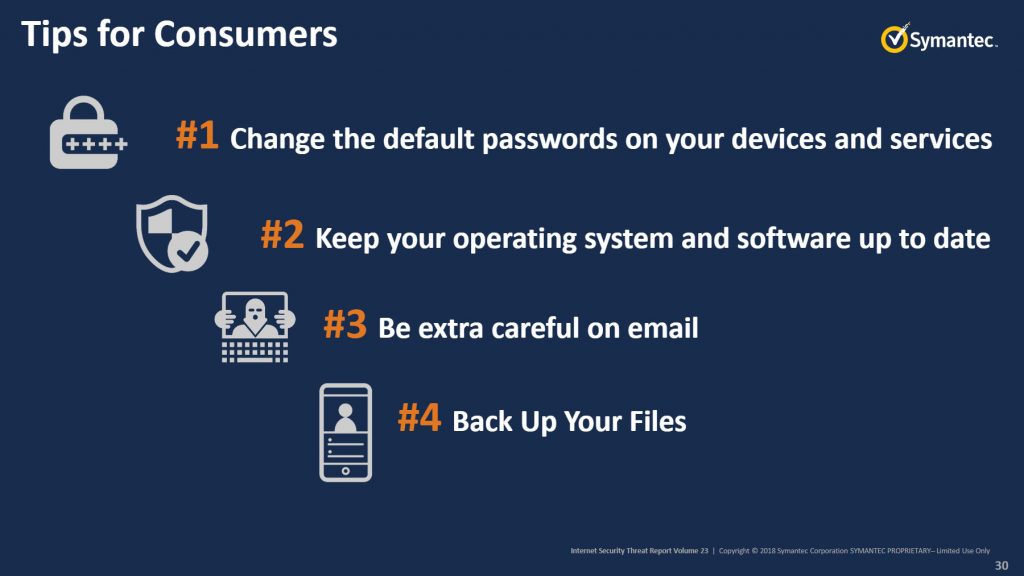
What can you do?
The most important thing is to keep your systems updated. Updated software and operating systems often come with patches that fixed exploits that can be taken advantage of by cybercriminals. Default passwords must also be changed, as they are an easy target to even the greenest of attackers. Do not simply click on email links or attachments unless they come from a trusted source. Also, always keep a backup, in case you do fall victim to an attack and your data is inaccesible. These tips also apply to connected businesses.
Pokdepinion: Security is not my strong field when I myself do not really apply most of the tips I am supposed to follow. But it’s interesting to see Malaysia ranks pretty high in terms of ransomware and cryptominers, which points to either Malaysians being more gullible to cryptojacking, or there are a lot of miners in Malaysia.






















































Leave a Response