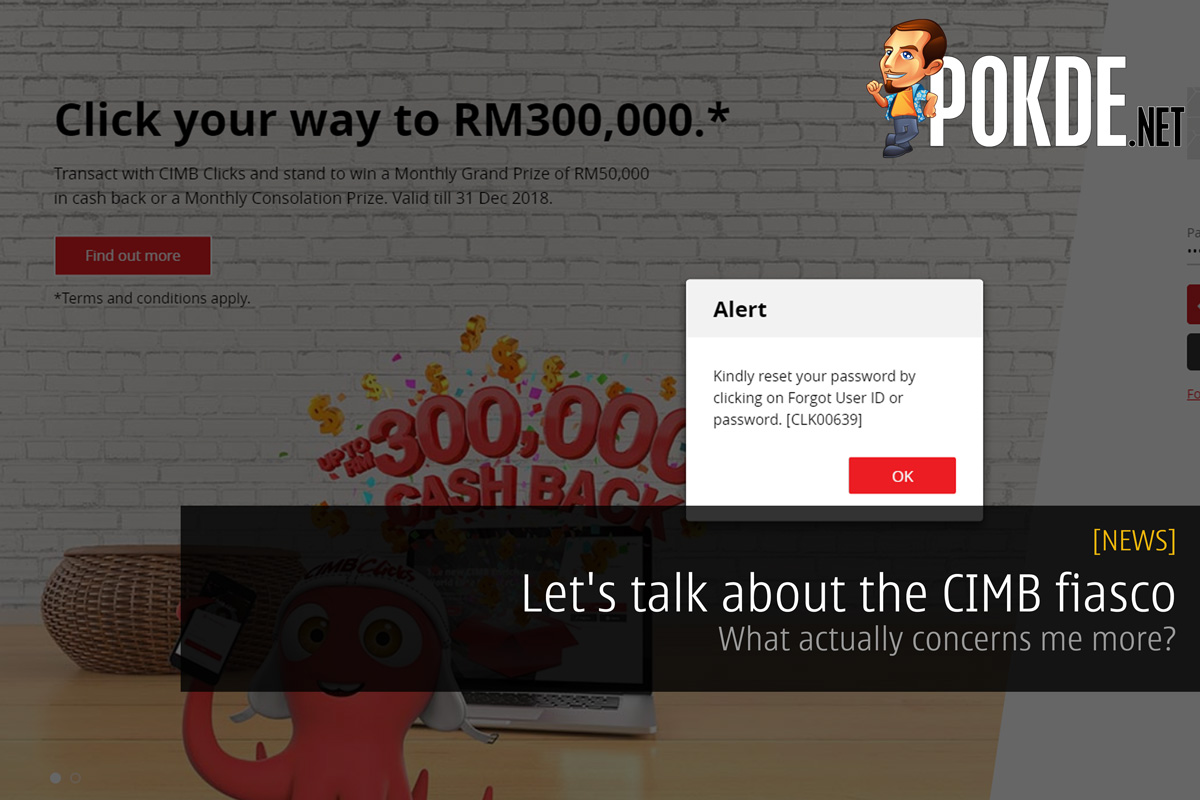
Let’s talk about the CIMB fiasco – What actually concerns me more?
There has been a rise in panic towards the recent so called CIMB security flaw. We have also updated the article with CIMB’s official statement to clarify what actually happened. In fact, our brothers at Nasi Lemak Tech has crafted a beautiful explanation of what it was actually all about. Now, let’s get three points clear:
- I am not a professional security expert, and my views are coming from a programmer’s perspective
- Security and convenience don’t go hand-in-hand and it’s the FIRST thing that needs to be considered for any online development
- We’re talking about banking institution of which every bit of security is of the utmost importance
For years, I’ve practiced keeping a minimum of 9 characters for my password, if not more and across the board, on average my password spans 12 characters. This has bugged me for a very long time that CIMB did not allow me to set any password longer than 8 characters before and was THE only password that I had in 8 characters. Hence, their latest movement towards minimum 8 characters and jacking up the maximum characters to 20 is actually plausible.
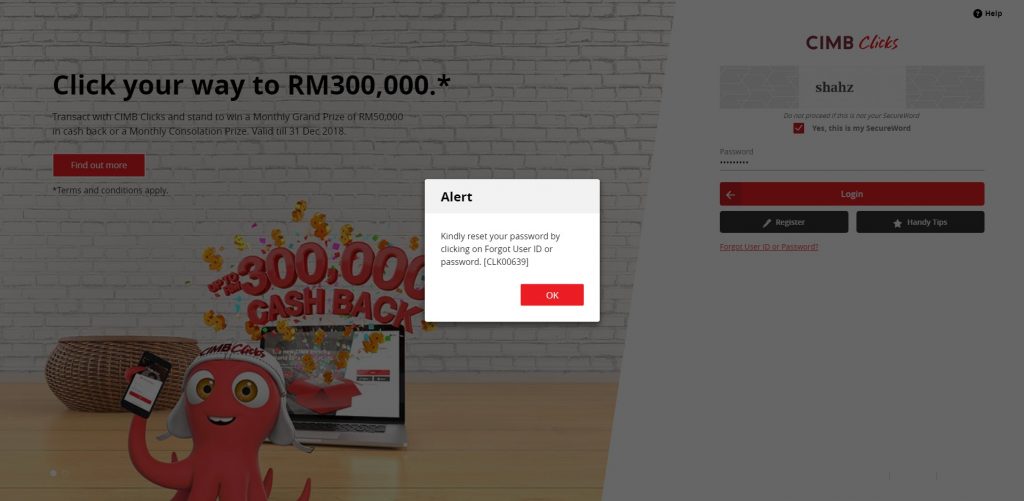
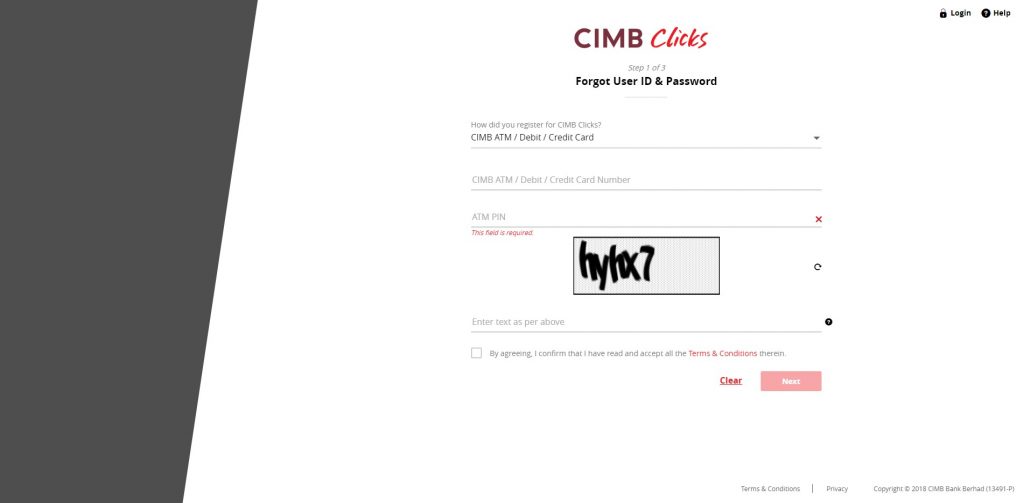
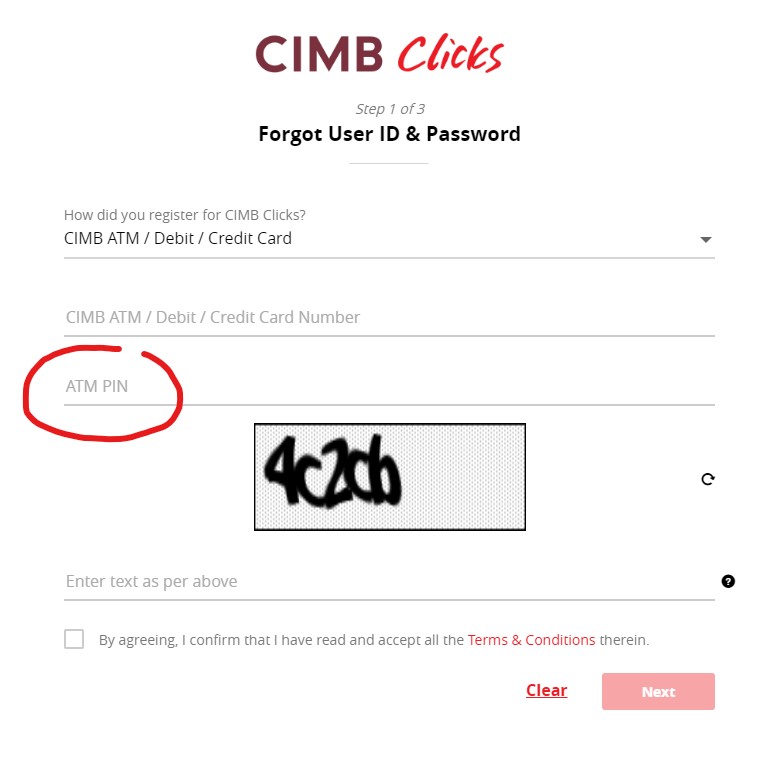
So when you login to your CIMBclicks now, upon a successful login session, you will be prompted to change your password. This is where things become a little worrying for me. Subsequent to this, you are asked to identify how did you register for your CIMB account:
At this point, CIMB is requesting you to validate your account to which we will be choosing “CIMB ATM / Debit / Credit Card“. You insert your card number, the ATM PIN number, captcha code, agree to the terms, and then hit submit. All looks normal right?
Except, it doesn’t look normal. CIMB requests for your PIN number here. Which means, once you submit the form, the card number and the PIN are carried together with the HTTP POST body (over AJAX since CIMB uses Angular for front-end). This is then sent to the CIMB servers for validation, upon which you would be able to reset your password.
How is this abnormal, you ask? It scares even more that nobody else in our office managed to identify the problem. I’ve been in a lengthy discussion with the good guys at Nasi Lemak Tech and here’s what we have to say about it.
You see, your PIN (Personal Identification Number) is YOUR personal identifier which even the banks are NOT supposed to know.
- When you get your ATM card, you slot the card into the card reader and you set your temporary PIN which you are requested to change it again later at the ATM.
- When you registered e-banking for the first time, you have to pay a visit to the bank, insert your card, validate the PIN and then a temporary PIN is issued for your usage.
- When you do a VISA transaction using wave, you can just tap the card and get done with it, but if you want to use the PIN, you MUST insert the card into the terminal first, before entering the PIN.
As you can see, you can never eliminate the need to have your card physically before using your PIN. This is because, the PIN is stored in the card. When it is needed, the server sends an encrypted string to the machine, requesting the PIN to unlock the secure container. Once the PIN is entered, the validation happens on the machine level itself where it checks against the stored PIN on the card (of course, encrypted). When everything matches, the transaction details are carried with a verified payload back to the servers. This is how the process is supposed to work.
However, in the case of CIMB password reset, there is no physical card contact. We submit the PIN and suddenly the validation happens. This means that CIMB is storing our PIN numbers on their servers and this is something very seriously worrying.
Pokdepinion: If the validation can take place in the back-end, there is a possible way to find your PIN and I can safely (pun intended) say, your Personal Identification Number, is not Personal after all?










































Is the pin your regular atm pin or is it a one time pin that you need to request for via atm?
If user has to go to an atm, and generate a one time pin for a reset pw transaction, that would be ok.
The one that is needed above is the regular ATM PIN.. Not a one time pin.
Same goes to m2u. Their forgot pwd func does ask for card no n atm pin.
there’s such a thing as an online pin https://security.stackexchange.com/questions/104076/how-does-a-debit-credit-card-reader-verify-the-pin-so-quickly