Intel faces new batch of MDS vulnerabilities affecting even the latest 9th Generation Intel Core processors
Intel has been facing one security flaw after another, with the latest being a whole series of them classified as MDS (microarchitectural data sampling) attacks. RIDL (Rouge In-Flight Data Load) and Fallout are the two new vulnerabilities identified on Intel CPUs. These vulnerabilities are pretty similar to Meltdown and Spectre, with them taking advantage of Intel’s speculative execution to grab secure data in the buffers between the processor cores and its cache.
Cristiano Giuffrida, one of the researchers in the VUSec group at Vrije Universiteit Amsterdam who discovered the MDS attack, has this to say about the MDS vulnerabilities:
“It’s kind of like we treat the CPU as a network of components, and we basically eavesdrop on the traffic between them. We hear anything that these components exchange.”
The data that can be stolen by attackers exploiting these vulnerabilities include passwords and encryption keys, which may pose a serious issue for people working with secure data. The researchers suggests disabling HyperThreading on Intel CPUs, but Intel does not recommend doing so. Intel considers the threat to be “low to medium”, while the researchers has ranked it to be “relatively significant”.
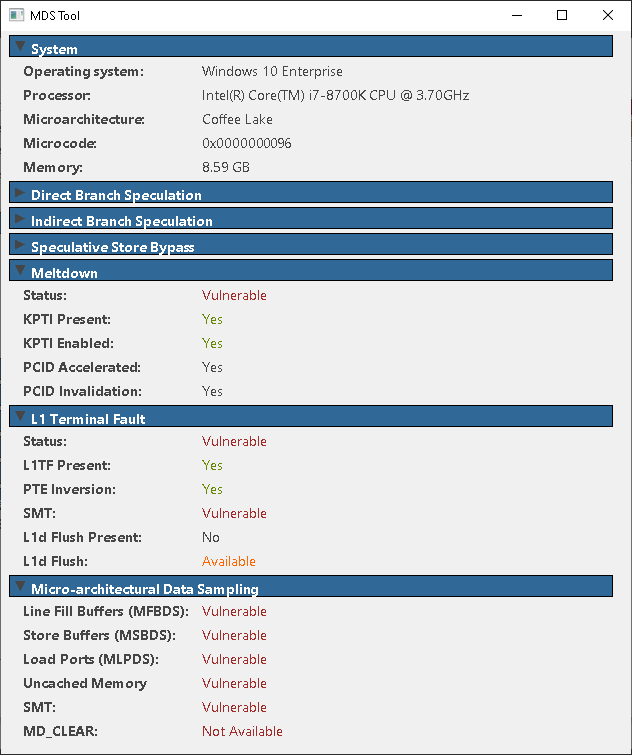
The patch for the MDS attack vulnerability is expected to see servers hit by a performance decrease of around 9%, while home PCs will probably not be too affected by it. You can check if your PC is vulnerable to these MDS attacks by downloading a tool offered on mdsattacks.com.
As of now, AMD and ARM processors do not exhibit this vulnerability, and it appears to be an Intel-exclusive one.
Pokdepinion: Well, I wonder how many more vulnerabilities will Intel have to patch, and how much performance will we lose in the end…















































Leave a Response